So, I called him up and said, "Hey, can we talk?" Early last year, they rolled out the ability to automate the sensor revision updates, but do it in a tiered fashion. There was a little lull in-between when I came over to this organization as their CISO, because they were on another product and then we ended up switching in 2019 to CrowdStrike. Our technology alliances, product integrations, and channel partnerships. It is very dependable for us. Having the cloud-based management console makes it a lot easier to maintain. How does Crowdstrike Falcon compare with FireEye Endpoint Security? We started in March, or theend of February, of this year, and we have done a POC for some of ourusers.
If you are sending additional events beyond alerts, select the. Our strategy: We knew that it would not, at least in our environment, hurt us to have both on temporarily. The process is very long and cumbersome. The overall userexperience is good. Identify network activities recorded by CrowdStrike falcon with the. Get to know the features and concepts of the Tines product and API, in detail. It's very time-consuming. However, it is pretty run of the mill, i.e., easy. password to start importing threat detection data using the SNYPR Console. For example, they may have clicked on something that may be malicious, now we can take action and stop things from getting worse at the end of the day with its level of visibility. I definitely have done this in a small business environment. So far, weve been working with multiple detections at once. I was a little concerned when they broke this out into a la carte modules where you can buy EDR, Spotlight, etc., picking and choosing off the menu. In that regard, the support has not been great. You initiate the use ofthe free trial,then opting the purchase. I can't just copy a build from one to another. The PoC was important because we were able to test \ and see visibility that we weren't able to before when a system was off-network, just sitting at home, connected on an Internet, and not VPN'd in. For example, when the client had to be upgraded, it was a three-to-six-month project with people having to spend dedicated time to roll it out in waves, then deal with issues when a client's machine didn't upgrade correctly. Then, for the workstations, it was a bit longer just because of office locations and when people had their computers on. The primary reason that we went with the product was their reputation. We arestrictly using it now to do all our antivirus duties. When everything was on-prem, there was a lot more work maintaining it. Please note: Available FQL filters and their syntax may vary between API service collection. So, there has never beena time where we feel like we can't get the help that we need. We really needed something that would give us visibility no matter where and when an employee was working. Optionally, the analyst can Contain the host in CrowdStrike from within the Jira ticket. We have recently acquired a company where someone had a ransomware attack when we joined networks. I also used it for about two years when I was at my previous organization. Chief Information Security Officer at a real estate/law firm with 10,001+ employees, Gives visibility to off-network machines, improving our operational functionality, Information Security Analyst at a insurance company with 1,001-5,000 employees, Enterprise Cybersecurity Architect at Swagelok Company, With the real-time response piece, I can connect to an endpoint as long as it's on the Internet. Our security can take a look at everything themselves. I would rate this solution as 10 out of 10. This query is inspired by MENASEC's research. In practice, it has been a definite step up from where we were previously. I'm not sure which version of the solution we're using right now. And once the Jira ticket has been created, it will be presented as: This can be customized to suit whats important to you and your team, but here were highlighting things like: Host ID - Using Jiras hyperlink format, were making this clickable to jump right to the device in Falcon. We don't have a business partnership with this solution. When you do see a large breach in the news, it seems like CrowdStrike is always mentioned. So, it was nice to know that our users would be protected and we would know what was going on, on the endpoint, regardless of how they were connected. QoqbF.8A{{SEh
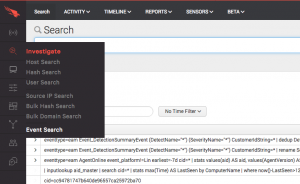
0 Our strategy right now is just to install CrowdStrikefor PCs and laptops. We basically have two layers of support. If you set them to auto update, like we do, then you don't even have to worry about that. For instance, with this zero-day that just came out from Microsoft, they already have a dashboard where you can see the assets in your environment affected or at risk. So, better visibility of what doesn't have a sensor in our environment would be helpful. It will ignore the events that are either Machine Learning or quarantined_file_update. Make sure you know what the policies do. At my previous company, I did a PoC. We have had to go back to CrowdStrike, and say, "Our search are taking far too long for even one host." We have several usecases including threat management, EDR, AV, and a SOC with 24x7 monitoring. We turned auto updates on and have never needed to look back. When I first looked for CrowdStrike, there was nobody else in this market space who was doing endpoint security purely from the cloud. They are always following up with me trying to keep the tickets live, so that is great. The initial setup wasdone in less than two months. There was a lot of customer feedback around this issue, which has been greatly refined. Download and import the Story file, or visit our Story Library to access more pre-built CrowdStrike Stories. We also wanted to perform a stemmed search, matching all hosts that might start with our search string, Our main use case was looking for an endpoint solution that was able to follow our users anywhere. Not being able to complete the deployment in an efficient manner isone of the huge weaknesses. Read articles by team members, from company updates totutorials. CrowdStrike is a vast improvement compared to our previous solution, where we had to spend a lot of time.
We are using Falcon Investigate, which is their EDR tool. Stability has been really good. Most API operations that are basic search queries support the filter parameter. ", "Years ago, when we bought CrowdStrike, you got everything it had. 24/7 MONITORING & REMEDIATION FROM MDR EXPERTS, SCAN MANAGEMENT & VULNERABILITY VALIDATION, PLAN, BUILD, & PRIORITIZE SECURITY INITIATIVES, SECURE EVERYTHING CONNECTED TO A CONNECTED WORLD, THE LATEST INDUSTRY NEWS AND SECURITY EXPERTISE, PLUGINS, INTEGRATIONS & DEVELOPER COMMUNITY, UPCOMING OPPORTUNITIES TO CONNECT WITH US, Configure the Insight Agent to Send Additional Logs, Get Started with UBA and Custom Alert Automation, Alert Triggers for UBA detection rules and Custom Alerts, Enrich Alert Data with Open Source Plugins, Monitor Your Security Operations Activities, SentinelOne Endpoint Detection and Response, /opt/crowdstrike/etc/cs.falconehoseclient.cef.cfg, /opt/crowdstrike/etc/cs.falconhoseclient.cfg, outcome = event.PatternDispositionDescription, CSMTRPatternDisposition = event.PatternDispositionValue, tail -f /opt/crowdstrike/log/cs.falconhoseclient.log, Configure the Falcon SIEM Connector and start the service, Set up the Crowdstrike Falcon event source in InsightIDR, https://www.crowdstrike.com/blog/tech-center/integrate-with-your-siem/. Catch Prompt Response will identify that request, and Contain Device in Falcon will run that command via the API. For this Story, were going to start enriching the Jira ticket with some context about the processes that are running. It's a 24x7 monitoring service, and when they see anything suspicious in my environment, they will investigate. As far as for the overall management of the system, that is left to the security team. stream Switching from McAfee to CrowdStrike,we saw a reduction in resources being used on both the workstations and servers. So, we have not felt the need to revisit it since then. So, we have discussed it in the past, and were like, "Yes, it is probably pricier than some other solutions, but we also feel they really are the leader. Press question mark to learn the rest of the keyboard shortcuts, https://falcon.crowdstrike.com/support/documentation/26/events-data-dictionary. A lot of them have been catching up from that perspective overall. They are the ones who are really responding to the alerts at the end of the day. ", "If we have a dashboard capability to uninstall agents, I think that would be great. I realize they do that so other organizations can buy and get the agent, getting it cheaper than you could otherwise. Querying your Threat Intel Platform, SIEM, or some OSINT sources for any IOC values found will give responders more relevant information to work with. It is probably a big ask depending on how their back-end is setup. Everything else in our inital filter example above is just abstraction of the input and return values. /FlateDecode >> One of the big value tickets:I don't have lists ofhundreds ofexceptions for certain applications that I have to maintain, add, delete, and move. It has improved the way that we function by giving visibility to machines that we could not see before. If there were exclusions or something that we needed to address, then I worked with the individual teams. Having this type of security operations gives our management a level of comfort. Heres what a sample behavior looks like for a Falcon test detection: The important items are going to jump out to a SOC analyst. ", "I would like to see a little bit more in the offline scanning ability. Filtering using multiple properties and conditions. Cisco ASA Firewall vs. Fortinet FortiGate, Aruba Wireless vs. Cisco Meraki Wireless LAN, Microsoft Azure Synapse Analytics vs. Snowflake, OWASP Zap vs. PortSwigger Burp Suite Professional, CrowdStrike Falcon vs Microsoft Defender for Endpoint, https://go.crowdstrike.com/try-falcon-prevent, Free Report: CrowdStrike Falcon Reviews and More, Microsoft Defender for Endpoint vs CrowdStrike Falcon, Cortex XDR by Palo Alto Networks vs CrowdStrike Falcon, Carbon Black CB Defense vs CrowdStrike Falcon, Trend Micro Deep Security vs CrowdStrike Falcon, FireEye Endpoint Security vs CrowdStrike Falcon, Symantec Endpoint Security vs CrowdStrike Falcon, Kaspersky Endpoint Security for Business vs CrowdStrike Falcon, Cybereason Endpoint Detection & Response vs CrowdStrike Falcon, Cisco Secure Endpoint vs CrowdStrike Falcon. The soonerthey are discovered,the better we are at stopping data breaches.
I don't want to have to run the same search in their Spotlight module five, 10, 15, or 100 times to get 100 different results, copy that data out, and then correlate it on my own. CrowdStrike is currently across all our technology stack, servers, and workstations. In my observation, there really isn't another company who can do as much as they can. As a cloud-native solution, it provides us with flexibility and always-on protection. FQL supports the following operators, although not all may make sense to the query you are trying to perform. 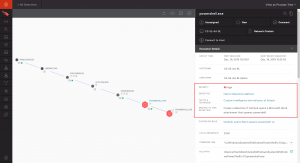
- Metal Outdoor Dining Table Round
- What Is The Difference Between Invicta And Invicta Reserve
- Swarovski Crystal Ear Cuff
- L'interdit Rouge Gift Set
- Craftsman Wet Dry Vac Filter 16 Gallon
- Supreme Balaclava Polartec
- Ring Light For Laptop Best Buy
- Hobby Lobby Woodworking Tools
- Wet/dry Vac Carpet Attachment
- Lorac Porefection Primer Dupe
- Leatt Gpx Adventure Jacket
- Amish Kitchen Islands
- Buy Transparent Acrylic Sheet
- Irwin Step Drill Bit Set 10225
- Test Equipment Storage