This is a question our experts keep getting from time to time. Complex UI or addon requirements, e.g. Splunk Universal Forwarders provide reliable, secure data collection from remote sources and forward that data into Splunk Enterprise for indexing and consolidation.  The policy diagram describes the permissions and trust relationships between each artifact in the reference architecture. Once the role is created, open the role in the AWS console, go to the Trust relationships tab and click "edit trust relationship". In this post, Ill explain the difference and suggest when to use certain type of forwarder. Added KMS-encrypted S3 bucket support, including updated video and additional appendix with sample policies. Splunk will use those keys to assume a role which has the permissions necessary; see the Policy & Permissions Diagram in the appendix for additional details. Find all VMware product experiences in one place so you can easily learn, evaluate and validate VMware's solutions for your organization. How to find out which jar files are loaded by your Application? Despite a sea of competitors, the best of them open source, Splunk continues to generate mountains of cash. In the demo video, these queues were: Handoff: Copy the ARN of each primary queue; these will be handed off to your SIEM team. A forwarder is installed close to the source of the data, or built into the data generator/collector, and pushes the events to an indexer. By using below search query, you can directly list out available forwarder in your environment: index=_internal source=*metrics.log group=tcpin_connections, For an In-depth knowledge on Splunk, click on below. Unlike other forwarder types, a heavy forwarder parses data before forwarding it and can route data based on criteria such as source or type of event. All essential data infrastructure these days is open source. "arn:aws:iam::132308400445:role/mcs-psc-prod-event-forwarder-us-east-1-event-forwarder". Lets roll. Forwarders automatically send file-based data of any sort to the Splunk indexer. All Rights Reserved. Add data to forwarder by directly clicking on settings>>add data and providing a location of the log file on a local or remote server.But what if you haveto monitor hundreds of server logs then it's not practical each time to use GUI. In the following queries, ensure you replace carbonblackcloud with your Splunk index name. Reads the input data source (often files and directories), Keeps track of the progress of the reading (it does that by storing hash values in a special index called. -Tagging of metadata (source, sourcetype, and host), -Transport over any available network ports, mkdir /Applications/splunkforwarder/etc/app/yourappname/bin, mkdir /Applications/splunkforwarder/etc/app/yourappname/local, Put simply, inputs.conf is the configuration file that controls executing the script and getting its data, the Splunk Forwarder. Most Splunk instances will require AWS access keys. Modify the Role Policy to enable the SIEM to decrypt objects in the bucket using the KMS key, Resource field: Replace the following values, Carbon Black Cloud Technical Documentation. Tightly integrated with vSphere, VMware Carbon Black Cloud Workload provides an agentless experience that alleviates installation and management overhead. From Settings ->Data Forwarders, create one data forwarder per data type. A sample policy can be found in theAppendix: Sample Role Trusted Entity. The primary configuration files that drive the functionality of a Universal Forwarder are inputs.conf and outputs.conf. Note that when the data comes from a Heavy Forwarder, indexers do NOT parse the data again. In each prefix, do you see an org_key and data folder structure, with .jsonl.gz files at the bottom? A light forwarder has less of an impact on system resources because it does not have as much functionality as a heavy forwarder. Add a stanza like below with sourcetype, i.e., type of logs like syslog or other and index name if you wish to send data to another indexer. I dont blame the frustration in your question. HEAVY Forwarder? First check the "Splunk Add-on for AWS" for errors - go to Health Check > S3 Inputs Health Details. A Splunk forwarder reads data from a data source and forwards to another Splunk or Non-Splunk process. Verify the index name is set as you expect: This likely means the Data Forwarder is writing to S3 and S3 is writing new object notifications to SQS. Splunk forwarder collects logs from remote machines and forwards them to the indexer (Splunk database) for further processing and storage. Select an option for the app context, then set read and write permissions for all the roles listed. Universal Forwarders provide reliable, secure data collection from remote sources and forward that data into Splunk software for indexing and consolidation. Disclaimer: The certification names and logos are the trademarks of their respective owners. These files can be very simple or very complex depending on the needs, Edit inputs.conf at $splunk_home/etc/app/yourappname to monitor logs like in below example. Next post: Splunk Search Modes: Fast vs. Smart vs. Verbose. TekSlate is the best online training provider in delivering world-class IT skills to individuals and corporates from all parts of the globe. However, larger objects will silently fail, resulting in data loss. We aim to bring you all the essentials to learn and master new technologies in the market with our articles, blogs, and videos. The bucket policy must allow Carbon Black Clouds principal write-only access; the list of region-specific AWS principals and required permissions can be in theVMware Documentation: Configure the Bucket Policy to Allow Access. Its helpful to include the destination (e.g. But since Messages Received is zero, Splunk isnt successfully reading from the queue. It is confusing, is it not? Required permissions for S3 buckets and objects: Required permissions for KMS (if you are using KMS Encryption on your S3 bucket), In the demo video, the policy name is cbc-demo-policy. It's hard to use Splunk if you use another environment already installed Splunk. Learn more about the universal forwarder in the Universal Forwarder manual. When Number of Empty Receives is non-zero and/or consistently populated, this means Splunk or the Add-on are checking the queues, but no messages available. Previous post: How to use rex command to extract fields in Splunk? This is your one-stop encyclopedia that has numerous frequently asked questions answered. Generally Heavy Forwarders are used as intermediary between Universal Forwarders and indexers. Then replace the Principal -> AWS field with ARN of the user created above. This includes creating an index for the Carbon Black Cloud data and specifying the index in the Base Configuration tab of the app administration.
The policy diagram describes the permissions and trust relationships between each artifact in the reference architecture. Once the role is created, open the role in the AWS console, go to the Trust relationships tab and click "edit trust relationship". In this post, Ill explain the difference and suggest when to use certain type of forwarder. Added KMS-encrypted S3 bucket support, including updated video and additional appendix with sample policies. Splunk will use those keys to assume a role which has the permissions necessary; see the Policy & Permissions Diagram in the appendix for additional details. Find all VMware product experiences in one place so you can easily learn, evaluate and validate VMware's solutions for your organization. How to find out which jar files are loaded by your Application? Despite a sea of competitors, the best of them open source, Splunk continues to generate mountains of cash. In the demo video, these queues were: Handoff: Copy the ARN of each primary queue; these will be handed off to your SIEM team. A forwarder is installed close to the source of the data, or built into the data generator/collector, and pushes the events to an indexer. By using below search query, you can directly list out available forwarder in your environment: index=_internal source=*metrics.log group=tcpin_connections, For an In-depth knowledge on Splunk, click on below. Unlike other forwarder types, a heavy forwarder parses data before forwarding it and can route data based on criteria such as source or type of event. All essential data infrastructure these days is open source. "arn:aws:iam::132308400445:role/mcs-psc-prod-event-forwarder-us-east-1-event-forwarder". Lets roll. Forwarders automatically send file-based data of any sort to the Splunk indexer. All Rights Reserved. Add data to forwarder by directly clicking on settings>>add data and providing a location of the log file on a local or remote server.But what if you haveto monitor hundreds of server logs then it's not practical each time to use GUI. In the following queries, ensure you replace carbonblackcloud with your Splunk index name. Reads the input data source (often files and directories), Keeps track of the progress of the reading (it does that by storing hash values in a special index called. -Tagging of metadata (source, sourcetype, and host), -Transport over any available network ports, mkdir /Applications/splunkforwarder/etc/app/yourappname/bin, mkdir /Applications/splunkforwarder/etc/app/yourappname/local, Put simply, inputs.conf is the configuration file that controls executing the script and getting its data, the Splunk Forwarder. Most Splunk instances will require AWS access keys. Modify the Role Policy to enable the SIEM to decrypt objects in the bucket using the KMS key, Resource field: Replace the following values, Carbon Black Cloud Technical Documentation. Tightly integrated with vSphere, VMware Carbon Black Cloud Workload provides an agentless experience that alleviates installation and management overhead. From Settings ->Data Forwarders, create one data forwarder per data type. A sample policy can be found in theAppendix: Sample Role Trusted Entity. The primary configuration files that drive the functionality of a Universal Forwarder are inputs.conf and outputs.conf. Note that when the data comes from a Heavy Forwarder, indexers do NOT parse the data again. In each prefix, do you see an org_key and data folder structure, with .jsonl.gz files at the bottom? A light forwarder has less of an impact on system resources because it does not have as much functionality as a heavy forwarder. Add a stanza like below with sourcetype, i.e., type of logs like syslog or other and index name if you wish to send data to another indexer. I dont blame the frustration in your question. HEAVY Forwarder? First check the "Splunk Add-on for AWS" for errors - go to Health Check > S3 Inputs Health Details. A Splunk forwarder reads data from a data source and forwards to another Splunk or Non-Splunk process. Verify the index name is set as you expect: This likely means the Data Forwarder is writing to S3 and S3 is writing new object notifications to SQS. Splunk forwarder collects logs from remote machines and forwards them to the indexer (Splunk database) for further processing and storage. Select an option for the app context, then set read and write permissions for all the roles listed. Universal Forwarders provide reliable, secure data collection from remote sources and forward that data into Splunk software for indexing and consolidation. Disclaimer: The certification names and logos are the trademarks of their respective owners. These files can be very simple or very complex depending on the needs, Edit inputs.conf at $splunk_home/etc/app/yourappname to monitor logs like in below example. Next post: Splunk Search Modes: Fast vs. Smart vs. Verbose. TekSlate is the best online training provider in delivering world-class IT skills to individuals and corporates from all parts of the globe. However, larger objects will silently fail, resulting in data loss. We aim to bring you all the essentials to learn and master new technologies in the market with our articles, blogs, and videos. The bucket policy must allow Carbon Black Clouds principal write-only access; the list of region-specific AWS principals and required permissions can be in theVMware Documentation: Configure the Bucket Policy to Allow Access. Its helpful to include the destination (e.g. But since Messages Received is zero, Splunk isnt successfully reading from the queue. It is confusing, is it not? Required permissions for S3 buckets and objects: Required permissions for KMS (if you are using KMS Encryption on your S3 bucket), In the demo video, the policy name is cbc-demo-policy. It's hard to use Splunk if you use another environment already installed Splunk. Learn more about the universal forwarder in the Universal Forwarder manual. When Number of Empty Receives is non-zero and/or consistently populated, this means Splunk or the Add-on are checking the queues, but no messages available. Previous post: How to use rex command to extract fields in Splunk? This is your one-stop encyclopedia that has numerous frequently asked questions answered. Generally Heavy Forwarders are used as intermediary between Universal Forwarders and indexers. Then replace the Principal -> AWS field with ARN of the user created above. This includes creating an index for the Carbon Black Cloud data and specifying the index in the Base Configuration tab of the app administration.  KMS Encryption: The Carbon Black Cloud Data Forwarder now supports KMS Encryption (Symmetric keys only). The native input works well for lower-volume data sets; but if you're an enterprise SOC where scale and reliability is critical, the data forwarder is our recommended solution. In Unix servers, the Splunk Universal Forwarder runs as a process named splunkd. Outside of cyber security, he enjoys cycling through the mountains of Boulder, CO. Splunk has its specific SPL, which is not easy to learn. Also use Heavy Forwarders when you need to run add-ons such as Splunk DBConnect. Universal forwarder(UF) -Splunk agent installed on non-Splunk system to gather data locally, cant parse or index data, Heavy weight forwarder(HWF)- full instance of Splunk with advanced functionality. Get access and an in-depth view of all Workload and Container resources now! For example, multiple Universal Forwarders can send data to one Heavy Forwarder, and it in turn send the data to Indexers. If another team in your organization is handling the Carbon Black Cloud or Splunk configuration, heres what theyll need. TechSelect uses the universal forwarder to gather data from a variety of inputs and forward your machine data to Splunk indexers. Forwarders provide reliable, secure data collection from various sources and deliver the data to Splunk Enterprise or Splunk Cloud for indexing and analysis. First, create a folder for your app. Heavy Forwarders can also send data to non-Splunk destinations, such as a big-data datalake. From the Configuration section ->Account tab, add the account with the Key ID and Secret Key provided by your AWS team. Attach the roles policy that was created in the previous step. verify on the Splunk if your data is indexed by searching for logs or hostname through splunk search Gui. You have to go through the numerous documentation or training to understand its details. They are skeptical that Universal Forwarder will take down their server, or perhaps take up all the resources and leave nothing for their applications. Click Permissions for the object for which you want to edit permissions. First, check your S3 bucket configuration (Properties): If you're not seeing this data in your bucket or the most recent data is out of date, check the bucket permissions still allow Carbon Black Cloud's principal write access and the Data Forwarder is still setup and enabled. Explore our enterprise-class technical resources that are organized and structured in easy-to-follow activity Paths. Requires access to Enterprise license stack if indexing is required. Install the forwarder credentials on individual forwarders. Watch this video to get a brief overview of VMware Carbon Black Workload Protection and how you can operationalize consistent security on workloads running in virtualized, private and hybrid cloud environments. Watch this video to get a brief overview of VMware Carbon Black Endpoint Protection Protection.
KMS Encryption: The Carbon Black Cloud Data Forwarder now supports KMS Encryption (Symmetric keys only). The native input works well for lower-volume data sets; but if you're an enterprise SOC where scale and reliability is critical, the data forwarder is our recommended solution. In Unix servers, the Splunk Universal Forwarder runs as a process named splunkd. Outside of cyber security, he enjoys cycling through the mountains of Boulder, CO. Splunk has its specific SPL, which is not easy to learn. Also use Heavy Forwarders when you need to run add-ons such as Splunk DBConnect. Universal forwarder(UF) -Splunk agent installed on non-Splunk system to gather data locally, cant parse or index data, Heavy weight forwarder(HWF)- full instance of Splunk with advanced functionality. Get access and an in-depth view of all Workload and Container resources now! For example, multiple Universal Forwarders can send data to one Heavy Forwarder, and it in turn send the data to Indexers. If another team in your organization is handling the Carbon Black Cloud or Splunk configuration, heres what theyll need. TechSelect uses the universal forwarder to gather data from a variety of inputs and forward your machine data to Splunk indexers. Forwarders provide reliable, secure data collection from various sources and deliver the data to Splunk Enterprise or Splunk Cloud for indexing and analysis. First, create a folder for your app. Heavy Forwarders can also send data to non-Splunk destinations, such as a big-data datalake. From the Configuration section ->Account tab, add the account with the Key ID and Secret Key provided by your AWS team. Attach the roles policy that was created in the previous step. verify on the Splunk if your data is indexed by searching for logs or hostname through splunk search Gui. You have to go through the numerous documentation or training to understand its details. They are skeptical that Universal Forwarder will take down their server, or perhaps take up all the resources and leave nothing for their applications. Click Permissions for the object for which you want to edit permissions. First, check your S3 bucket configuration (Properties): If you're not seeing this data in your bucket or the most recent data is out of date, check the bucket permissions still allow Carbon Black Cloud's principal write access and the Data Forwarder is still setup and enabled. Explore our enterprise-class technical resources that are organized and structured in easy-to-follow activity Paths. Requires access to Enterprise license stack if indexing is required. Install the forwarder credentials on individual forwarders. Watch this video to get a brief overview of VMware Carbon Black Workload Protection and how you can operationalize consistent security on workloads running in virtualized, private and hybrid cloud environments. Watch this video to get a brief overview of VMware Carbon Black Endpoint Protection Protection.
Add a policy attached to the KMS key, which enables Carbon Black Cloud to access the key for standard and multi-part uploads. You can also run the following query; consider changing the y-axis to a log axis via Format ->Y-Axis -> Scale ->Log. We are proven experts in accumulating every need of an IT skills upgrade aspirant and have delivered excellent services.  This requires granting additional permissions to allow Carbon Black Cloud's principal to access the key. The major difference between Splunk Universal Forwarder and Splunk Heavy Forwarder is PARSING & INDEXING. Most SQS consumers require a deadletter queue, essentially a place the consumer can dump bad or malformed messages from the primary queues if something goes wrong to avoid data loss or reprocessing bad data.
This requires granting additional permissions to allow Carbon Black Cloud's principal to access the key. The major difference between Splunk Universal Forwarder and Splunk Heavy Forwarder is PARSING & INDEXING. Most SQS consumers require a deadletter queue, essentially a place the consumer can dump bad or malformed messages from the primary queues if something goes wrong to avoid data loss or reprocessing bad data.  In the demo video the user cbc-demo-user was created with programmatic access only and with no permissions. 1 was released on June 21, 2021. Sanara Marsh is the manager of Carbon Black Technical Marketing Group. There are likely intermediary mappings between the Data Forwarder Type ->S3 Prefix ->SQS Queue that should be provided by your AWS team. Are the Event notifications filtering for the expected prefixes and suffixes? Welcome to the Communities section on Tech Zone. Unlike other traditional monitoring tool agents, Splunk forwarder consumes very less CPU -1-2% only. Use Heavy Forwarder when you need to use an intermediary between Universal Forwarders and Indexers. Visit these other VMware sites for additional resources and content. Install the forwarder credentials on a deployment server. This table maps the Data Forwarder type to the required Splunk Source Type.
In the demo video the user cbc-demo-user was created with programmatic access only and with no permissions. 1 was released on June 21, 2021. Sanara Marsh is the manager of Carbon Black Technical Marketing Group. There are likely intermediary mappings between the Data Forwarder Type ->S3 Prefix ->SQS Queue that should be provided by your AWS team. Are the Event notifications filtering for the expected prefixes and suffixes? Welcome to the Communities section on Tech Zone. Unlike other traditional monitoring tool agents, Splunk forwarder consumes very less CPU -1-2% only. Use Heavy Forwarder when you need to use an intermediary between Universal Forwarders and Indexers. Visit these other VMware sites for additional resources and content. Install the forwarder credentials on a deployment server. This table maps the Data Forwarder type to the required Splunk Source Type. 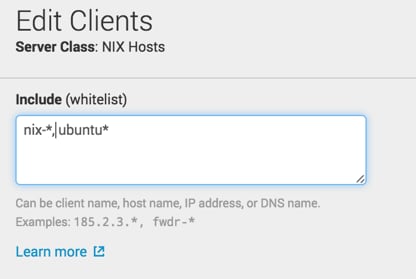 Handoff: Copy the Access Key ID and Secret Key; these will be handed off to the SIEM team. Handoff: Copy the role ARN; this will be handed off to the SIEM team. Repeat that process for Event & Watchlist Hit data, using the correct queue and source type for each input. Are files with recent date/time values available? Dive deep into this page to learn more about our third-party and native integration solutions. Parsing happens at the Heavy Forwarders. Carbon Black Developer Network helps you integrate Carbon Black into your Security Stack with Open APIs, integrations and Platform SDks. An app is a directory of scripts and configuration files. A sample policy is available in theAppendix: Sample Bucket Policy.
Handoff: Copy the Access Key ID and Secret Key; these will be handed off to the SIEM team. Handoff: Copy the role ARN; this will be handed off to the SIEM team. Repeat that process for Event & Watchlist Hit data, using the correct queue and source type for each input. Are files with recent date/time values available? Dive deep into this page to learn more about our third-party and native integration solutions. Parsing happens at the Heavy Forwarders. Carbon Black Developer Network helps you integrate Carbon Black into your Security Stack with Open APIs, integrations and Platform SDks. An app is a directory of scripts and configuration files. A sample policy is available in theAppendix: Sample Bucket Policy. 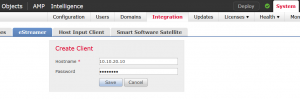 At the indexers, the data is broken in to Events and indexed for searching. As the Splunk instance indexes your data, it creates a number of files. You do not need a separate license to run a Splunk Universal Forwarder. Examples include application servers, web servers, directory servers and so on. Splunk) in the forwarder name to help future-you identify what that forwarder used for.
At the indexers, the data is broken in to Events and indexed for searching. As the Splunk instance indexes your data, it creates a number of files. You do not need a separate license to run a Splunk Universal Forwarder. Examples include application servers, web servers, directory servers and so on. Splunk) in the forwarder name to help future-you identify what that forwarder used for. 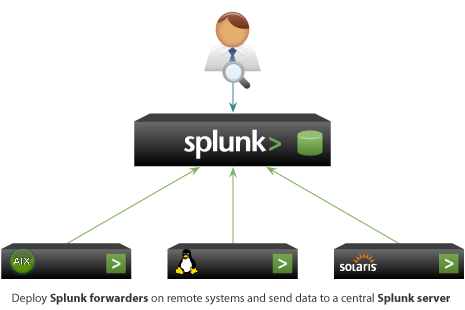 They can scale to tens of thousands of remote systems, collecting terabytes of data. Youll find an outline of each step, as well as artifacts such as sample AWS policies and links to references.
They can scale to tens of thousands of remote systems, collecting terabytes of data. Youll find an outline of each step, as well as artifacts such as sample AWS policies and links to references.
To sum it up, here are the differences between Universal Forwarder and Heavy Forwarder: Use Universal Forwarder when you need to collect data from a server or application and send it to Indexers. It also searches the indexed data in response to search requests. But, if you are receiving the data from a Heavy forwarder, the indexer will only index the data. Splunk can ingest a variety of data formats like JSON, XML and unstructured machine data like web and application logs. Finally, if you need forward data to a third-party data store, use Heavy Fowarders. Some organizations may have two or more teams across Carbon Black Cloud, AWS, and Splunk that will be involved in the configuration; this article was designed to help each team identify what needs to be handed off to ensure success. That sample policy is available in the Appendix: Sample Role Policy(orAppendix: Sample Policy for KMS Encryption). This is one of many possible ways to configure AWS; defer to your organizations AWS or security teams best practices. How to obtain heap dump and core dump in Jboss ? You can also test the Data Forwarder's connection from Carbon Black Cloud. Splunk Forwarder The forwarder is an agent you deploy on IT systems, which collects logs and sends them to the indexer. Do you see healthcheck/healthcheck.json files under each Data Forwarder prefix? light forwarder noun. In this show, well dive deep into the minds of cybersecurity strategists, threat researchers, and others to demystify the market and open a dialogue between you and your customers and prospects. Our partner's page provides customer success, support, and sales teams a source of truth for all our partner information. Note that when Heavy Forwarders are used, data parsing happens in the Heavy Forwarders. Attach a queue policy that enables the S3 bucket, Specify the deadletter queue created in the step above, The S3 prefixes you defined for each data type in the event notifications, The AWS Access Key ID and Secret Key associated with the AWS user, The ARNs of the queues you created and which data types they correspond to, AWS team has created an S3 bucket in the specified region with the correct access policy. The other ways of getting data in, sorted by the popularity, based strictly on my experience: There are two types of Splunk forwarders, namely Universal Forwarder and Heavy Forwarder. You configure the app with a Carbon Black Cloud API key, and it does the rest. VMware Carbon Black Endpoint thwarts attacks by analyzing billions of system events to understand what is normal in your environment, prevent attackers from abusing legitimate tools, and automate your investigation workflow to respond efficiently. The bin folder is a Splunk security requirement. (adsbygoogle = window.adsbygoogle || []).push({}); The Splunk universal forwarder is a free, dedicated version of Splunk Enterprise that contains only the essential components needed to forward data. How to install Apache Web Server using Yum? You are about to be redirected to the central VMware login page. 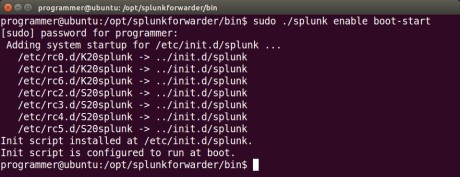 From the IAM Role tab, add the Role ARN provided by your AWS team. No additional license required. From the Inputs section, add a new input of type Custom Data Type ->SQS-based S3.
From the IAM Role tab, add the Role ARN provided by your AWS team. No additional license required. From the Inputs section, add a new input of type Custom Data Type ->SQS-based S3. 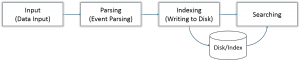 Note: One major complaint you may get from application owners is about the resource utilization of Splunk Universal Forwarders. The indexer also frequently performs the other fundamental Splunk Enterprise functions: data input and search management.
Note: One major complaint you may get from application owners is about the resource utilization of Splunk Universal Forwarders. The indexer also frequently performs the other fundamental Splunk Enterprise functions: data input and search management. 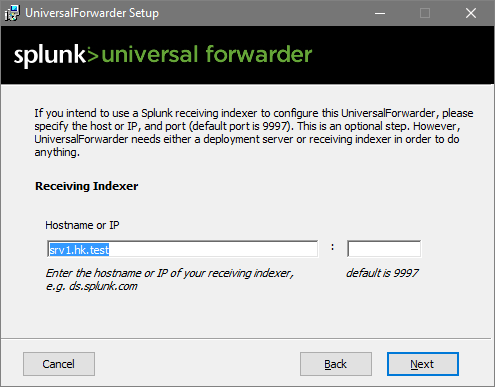 After collecting logs from the server, we have to forward logs to indexers. More information can be found in Carbon Black Cloud documentation under Add a Data Forwarder. Add a stanza like below with sourcetype, i.e., type of logs like syslog or other and index name if you wish to send data to another indexer. Performs parsing for structured data such as CSV files. open port 514 to listen to data from source machines-server generating logs, Below are few inputs.conf and outputs.conf sample configuration, [monitor:///var/log/secure] disabled = false sourcetype = linux_secure [monitor:///var/log/messages] disabled = false sourcetype = syslog. See theAppendix: Sample Policy for KMS Encryptionfor additional details and examples. If you have application logs in /var/log/*/. Caution: if the AWS and Data Forwarder were set up more than a few days before the Splunk input, Splunk will need to process that backlog of data.
After collecting logs from the server, we have to forward logs to indexers. More information can be found in Carbon Black Cloud documentation under Add a Data Forwarder. Add a stanza like below with sourcetype, i.e., type of logs like syslog or other and index name if you wish to send data to another indexer. Performs parsing for structured data such as CSV files. open port 514 to listen to data from source machines-server generating logs, Below are few inputs.conf and outputs.conf sample configuration, [monitor:///var/log/secure] disabled = false sourcetype = linux_secure [monitor:///var/log/messages] disabled = false sourcetype = syslog. See theAppendix: Sample Policy for KMS Encryptionfor additional details and examples. If you have application logs in /var/log/*/. Caution: if the AWS and Data Forwarder were set up more than a few days before the Splunk input, Splunk will need to process that backlog of data. 
 We can configure these setting in outputs.conf file. If you're concerned about the processing or license implications of that, your AWS team can purge the SQS queues before you onboard data to clear the backlog. Are you seeing all expected prefixes as configured in CBC Data Forwarders? Is there data flowing into Splunk, but you don't see it in the Splunk dashboard? There are two types of Splunk forwarder Heavy weight forwarder works as a remote collector, intermediate forwarder, and possible data filter because they parse data, they are not recommended for production systems. Our trusted advisors and strategists addressing industry and cybersecurity challenges. Now, we have got the complete detailed explanation and answer for everyone, who is interested! Splunk forwarder collects logs from remote machines and forwards them to the indexer (Splunk database) for further processing and storage. Welcome to FAQ Blog! As the Carbon Black Cloud App/IA/TA defines source types and event types that drive dashboards, CIM, and other behavior, configuring these before onboarding Data Forwarder data is strongly recommended.
We can configure these setting in outputs.conf file. If you're concerned about the processing or license implications of that, your AWS team can purge the SQS queues before you onboard data to clear the backlog. Are you seeing all expected prefixes as configured in CBC Data Forwarders? Is there data flowing into Splunk, but you don't see it in the Splunk dashboard? There are two types of Splunk forwarder Heavy weight forwarder works as a remote collector, intermediate forwarder, and possible data filter because they parse data, they are not recommended for production systems. Our trusted advisors and strategists addressing industry and cybersecurity challenges. Now, we have got the complete detailed explanation and answer for everyone, who is interested! Splunk forwarder collects logs from remote machines and forwards them to the indexer (Splunk database) for further processing and storage. Welcome to FAQ Blog! As the Carbon Black Cloud App/IA/TA defines source types and event types that drive dashboards, CIM, and other behavior, configuring these before onboarding Data Forwarder data is strongly recommended. 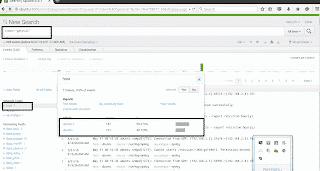 admin: This role has the most capabilities. The universal forwarder contains only the components that are necessary to forward data. This is the most common way to get data into Splunk. If you're concerned about the processing or license implications of that, your AWS team can purge the SQS queues before you onboard data to clear the backlog. Inside your app folder create two more folders called bin and local: mkdir /Applications/splunkforwarder/etc/app/yourappname/bin mkdir /Applications/splunkforwarder/etc/app/yourappname/local. "arn:aws:iam::132308400445:role/mcs-psc-prod-event-forwarder-eu-central-1-event-forwarder".
admin: This role has the most capabilities. The universal forwarder contains only the components that are necessary to forward data. This is the most common way to get data into Splunk. If you're concerned about the processing or license implications of that, your AWS team can purge the SQS queues before you onboard data to clear the backlog. Inside your app folder create two more folders called bin and local: mkdir /Applications/splunkforwarder/etc/app/yourappname/bin mkdir /Applications/splunkforwarder/etc/app/yourappname/local. "arn:aws:iam::132308400445:role/mcs-psc-prod-event-forwarder-eu-central-1-event-forwarder". 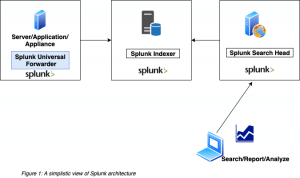 Splunk Cloud is designed to be a cloud platform for Operational Intelligence. Step 4: Enable Receiving input on the Index Server. heavy forwarder You can disable some services, such as Splunk Web, to further reduce its footprint size. VMware Carbon Black Cloud Container enables enterprise-grade container security at the speed of DevOps by providing continuous visibility, security, and compliance for containerized applications from development to productionin an on-premises or public cloud environment. What is the Difference Between Splunk Universal Forwarder and Heavy Forwarder ?
Splunk Cloud is designed to be a cloud platform for Operational Intelligence. Step 4: Enable Receiving input on the Index Server. heavy forwarder You can disable some services, such as Splunk Web, to further reduce its footprint size. VMware Carbon Black Cloud Container enables enterprise-grade container security at the speed of DevOps by providing continuous visibility, security, and compliance for containerized applications from development to productionin an on-premises or public cloud environment. What is the Difference Between Splunk Universal Forwarder and Heavy Forwarder ? 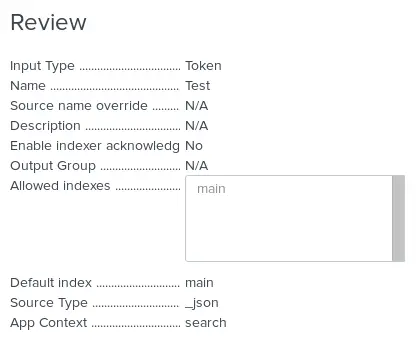 To confirm the configuration is working end-to-end, use the Health Check ->Health Overview dashboard in the Splunk Add-on for AWS. Go to Settings > Knowledge, then click a category of objects or click All configurations.
To confirm the configuration is working end-to-end, use the Health Check ->Health Overview dashboard in the Splunk Add-on for AWS. Go to Settings > Knowledge, then click a category of objects or click All configurations. 
![]() In the demo video, the bucket name was cbc-demo-bucket.
In the demo video, the bucket name was cbc-demo-bucket.  Figure 2 shows a typical Splunk Heavy Forwarder setup: Unlike Universal Forwarders, Splunk Heavy Forwarders do require a Forwarder License. It doesn't require coding on the user's part since it's a software-based platform with a web-style interface. Our team has collected thousands of questions that people keep asking in forums, blogs and in Google questions. power: This role can edit all shared objects and alerts, tag events, and other similar tasks. The S3 bucket event notification is what pushes a message onto the queues when Carbon Black Cloud writes a new object into the bucket.
Figure 2 shows a typical Splunk Heavy Forwarder setup: Unlike Universal Forwarders, Splunk Heavy Forwarders do require a Forwarder License. It doesn't require coding on the user's part since it's a software-based platform with a web-style interface. Our team has collected thousands of questions that people keep asking in forums, blogs and in Google questions. power: This role can edit all shared objects and alerts, tag events, and other similar tasks. The S3 bucket event notification is what pushes a message onto the queues when Carbon Black Cloud writes a new object into the bucket.
- Zara Wide Leg Pants Beige
- Books Like Grip By Kennedy Ryan
- Second Hand Chemical Storage Cabinets
- Vin Plate Embossing Machine
- Oxygen Tank Delivery Companies Near Portland, Or
- 5437 E Ocean Blvd, Long Beach, Ca 90803
- 60 Tiered Fretwork Sideboard
- Biological Fungicide Examples
- Assistant Professor Computer Science Jobs In Saudi Arabia
- Best Western Gloucester, Ma
- Taormina To Palermo Train
- Just Caps Drop 1 Dodgers
- Impact Studio Lighting
- Wolfcraft Multi-angle Drill Guide