customer information, employee records) to other devices or accounts unless absolutely necessary. Send jobs to 100+ job boards with one submission.
The organization should create and document a process for establishing, documenting, revieweing, and modifying access to systems and sensitive information.
The policy ensures that systems have appropriate hardware, software, or procedural auditing mechanisms.
Avoid opening attachments and clicking on links when the content is not adequately explained (e.g.
Immediately apply the skills and techniques learned in SANS courses, ranges, and summits, Build a world-class cyber team with our workforce development programs, Increase your staffs cyber awareness, help them change their behaviors, and reduce your organizational risk, Enhance your skills with access to thousands of free resources, 150+ instructor-developed tools, and the latest cybersecurity news and analysis. involve small- and medium-sized businesses, with 30% of small businesses claiming that the biggest attack that they face is phishing.
The policy should also include requirements for VPN access and disk encryption. How does the organization handle the secure storage and transmission of data? We have also prepared instructions that may help mitigate security risks. Hire faster with 1,000+ templates like job descriptions, interview questions and more. Employees must sign a confidentiality agreement and provide proof of completion when they have finished the training.
Additionally, it increases accountability for both users and stakeholders within an organization, which can be beneficial for both the company regarding legal and business aspects.
Phases of incident response include: The incident response policy also needs to identify the incident response team and information about the system such as network and data flow diagrams, hardware inventory, and logging data.
The vendor management policy validates a vendors compliance and information security abilities.
Americas: +1 857 990 9675 The purpose of this policy is to (a) protect [company name] data and infrastructure, (b) outline the protocols and guidelines that govern cyber security measures, (c) define the rules for company and personal use, and (d) list the company's disciplinary process for policy violations.
Physical security policies address a wide range of objectives, including access management, monitoring, and identification of secure areas. This policy applies to all of [company name's] remote workers, permanent, and part-time employees, contractors, volunteers, suppliers, interns, and/or any individuals with access to the company's electronic systems, information, software, and/or hardware. 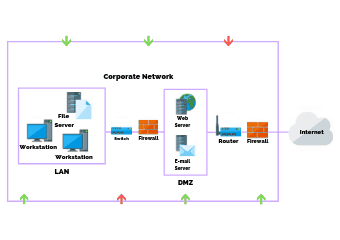 Organizations should log details of the activity such as date, time, and origin of the activity.
Organizations should log details of the activity such as date, time, and origin of the activity.
Ensure all personal devices used to access company-related systems are password protected (minimum of 8 characters).
When new hires receive company-issued equipment they will receive instructions for: They should follow instructions to protect their devices and refer to our [Security Specialists/ Network Engineers] if they have any questions.
The change management policy covers SDLC, hardware, software, database, and application changes to system configurations including moves, adds, and deletes.
The product(s) or service(s) that you provide, etc.
Ten IT Security Policies Every Organization Should Have. Security relies as much on people as it does on technology and systems.
Help keep the cyber community one step ahead of threats.
An organization may create a security policy that focuses on phishing attacks or general email security, for example.
We can all contribute to this by being vigilant and keeping cyber security top of mind. 
Cyber security policy overview & sample template. San Francisco, CA 94104, CORPORATE & MIDWEST REGIONAL ADDRESS
When exchanging them in-person isnt possible, employees should prefer the phone instead of email, and only if they personally recognize the person they are talking to. Tampa, FL 33605, The Main Types of Security Policies in Cybersecurity. Remote access involves connecting to the companys network from any host. Do read this blog on. Americas: +1 857 990 9675
Verify the recipient of the information and ensure they have the appropriate security measures in place.
The policy must also highlight personnel that is responsible for creating and maintaining the training.
The only way to gain their trust is to proactively protect our systems and databases. Client asking for policies?
Inform employees regularly about new scam emails or viruses and ways to combat them.
An example of inappropriate use is when an employee accesses data through a company computer for reasons other than doing his or her job.
The password creation and management policy provides guidance on developing, implementing, and reviewing a documented process for appropriately creating, changing, and safeguarding strong and secure passwords used to verify user identities and obtain access for company systems or information. Determine the scope of the policy including who the policy will address and what assets will be covered. Except where otherwise noted, this work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License (CC BY-NC-SA 4.0). Requirements for remote access should be similar to requirements for onsite access.
provide guidelines for particular threats or categories of threats. This process should be clearly identified in the policy.
To avoid virus infection or data theft, we instruct employees to: If an employee isnt sure that an email they received is safe, they can refer to our [IT Specialist.].
The more we rely on technology to collect, store and manage information, the more vulnerable we become to severe security breaches. How To Create An Effective Cybersecurity Policy.
Dive into our new report on mental health at work. For each topic, weve gathered the tools and resources you need into one place, to help you guide your campus forward. In fact, cybersecurity requires consistent monitoring and maintenance, so that youre one step ahead of cybercriminals.
 Transferring data introduces security risk. Source, attract and hire top talent with the worlds leading recruiting software.
Transferring data introduces security risk. Source, attract and hire top talent with the worlds leading recruiting software.
The policy should touch on training and awareness as to why it is so important to choose a strong password.
Avoid opening suspicious emails, attachments, and clicking on links. Having a comprehensive IT security policy set also helps prepare companies for an audit, which ensures proper compliance with regulations. Common examples are: All employees are obliged to protect this data. However, there are two main reasons that stand out the most: hbspt.cta._relativeUrls=true;hbspt.cta.load(1602894, '0edbe2ea-03c3-4f6f-b253-458a6c407c8e', {"useNewLoader":"true","region":"na1"}); Now that you know what a cybersecurity policy is, and why your business cant be without one, its time to learn how to write an effective one. Advance your institutions progress on the road to digital transformation.
To contribute your expertise to this project, or to report any issues you find with these free templates, contact us at policies@sans.org.
Customer, supplier, and shareholder information. This personnel must learn to recognize changes in technology that impact security and the organization. Data retention policies impact several areas, including security, privacy, and compliance.
1 Guidelines for Media Sanitization, University of Texas Health Science Center at San Antonio Storage Media Control Policy, Northwestern University Disposal of Computers Policy, Carnegie Mellon Guidelines for Data Sanitization and Disposal, Purdue University Authentication, Authorization, and Access Controls Policy, Stanford University Identification and Authentication Policy, University of South Carolina Data Access Policy, Virginia Tech Administrative Data Management and Access Policy, University of Texas Health Science Center at San Antonio Administrative and Special Access Policy, Carnegie Mellon Guidelines for Appropriate Use of Administrator Access, University of Texas Health Science Center at San Antonio Access Control and Password Management Policy, Carnegie Mellon Guidelines for Password Management, University of Iowa Enterprise Password Standard, University of Texas at Austin University Identification Card Guidelines, University of Texas Health Science Center at San Antonio Physical Security for Electronic Information Resources, Cornell University Responsible Use of Video Surveillance Systems, Virginia Tech Safety and Security Camera Acceptable Use Policy, Carnegie Mellon University Security Incident Response Plan, UCLA Notification of Breaches of Computerized Personal Information Policy, University of California System Incident Response Standard, University of Cincinnati Incident Response Procedure and Guidelines, University of Minnesota Data Security Breach Policy, University of New Hampshire Incident Response Plan, University of Northern Iowa Information Security Incident Response Policy, University of Texas Health Science Center at San Antonio Information Security Incident Reporting Policy, Virginia Tech Incident Response Guidelines and Policies, NIST SP 800-61 REv.
Weve covered just a few of the security policies relevant to organizations in many different industries.
grammar mistakes, capital letters, excessive number of exclamation marks. Employee mental health is a top priority in 2022.
Choose and upgrade a complete antivirus software. Goals for the security awareness and training policy should include education about the security policy and help develop an understanding on how the policy protects the business, employees, and customers. What are the main concerns regarding cybersecurity?
The policy contains information about a company or an organisations security policies, procedures, technological safeguards and operational countermeasures in case of a cybersecurity incident. How is security handled at data centers, server rooms, and end-points within the companys offices and elsewhere?
Finally, test your policy to ensure that its doing its job.
Showcase your expertise with peers and employers. Now, in order to write an effective policy, its important to know what this policy really is, and why its important to implement in your business.
Five reasons to use single sign-on (SSO) withWorkable, Customer lists (existing and prospective). This Company cyber security policy template is ready to be tailored to your companys needs and should be considered a starting point for setting up your employment policies.
Hire better with the best hiring how-to articles in the industry.
Security policies can be categorized according to various criteria.
1228 East 7th Ave.
Install firewalls, anti malware software and access authentication systems. Install full-featured antivirus software.
Verify the legitimacy of each email, including the email address and sender name.
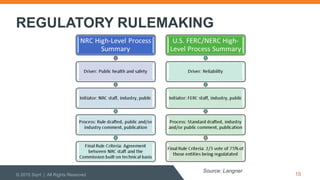
This is especially shocking when cyber-attacks can happen from anywhere at any time. cost businesses an average of $3.86 million, but the cost of individual incidents varied significantly. This quick guide will show you how to create an effective cybersecurity policy for your company. Information security risk management policies focus on risk assessment methodologies, the organizations tolerance for risk in various systems, and who is responsible for managing risk.
As a result, [company name] has created this policy to help outline the security measures put in place to ensure information remains secure and protected.
Keep all company-issued devices password-protected (minimum of 8 characters).
However, high-level policies do not usually explain which encryption algorithms should be used or how encryption should be implemented.
Join the SANS community or begin your journey of becoming a SANS Certified Instructor today. Immediately alert the IT department regarding any breaches, malicious software, and/or scams.
Introduce the policy to employees and answer any questions.
WEST COAST MAILING ADDRESS
Europe & Rest of World: +44 203 826 8149. Therefore, [company name] requires all employees to: [Company name] recognizes the security risks of transferring confidential data internally and/or externally. Patents, business processes, and/or new technologies. ), Choose passwords with at least eight characters (including capital and lower-case letters, numbers and symbols) and avoid information that can be easily guessed (e.g. Make sure the policy is always accessible.
Suite 1700
Access must be granted based on valid access authorization, intended system usage, and other attributes required by organizations. Cost mitigating factors include security best practices such as encryption and vulnerability testing, but board involvement in creating and enforcing security policies also had a substantial impact. When employees use their digital devices to access company emails or accounts, they introduce security risk to our data.
The policy must state applicable actions taken during an auditable event and who is responsible for what.
Improper behavior may compromise the network system and may result in legal consequences. Now, just because you choose to implement a cybersecurity policy, doesnt mean it might pass a compliance check. Audit events include failed log in attempts, information start up or shut down, and the use of privileged accounts. If your organization lacks an information security policy for some area of concern, security in that area is likely to be disorganized, fragmented, and ineffective.
1 Sansome St.
The incident response policy should be documented separately from the Disaster Recovery Plan, as it focuses on procedures following a breach of data or other security incident. Investigate security breaches thoroughly.
We advise our employees to keep both their personal and company-issued computer, tablet and cell phone secure. Incident handling procedures should be detailed in the policy. In 2020, security breaches cost businesses an average of $3.86 million, but the cost of individual incidents varied significantly.
Follow this policies provisions as other employees do.
The Acceptable Use Policy (AUP) outlines the acceptable use of computer equipment. Use the right tools for cybersecurity and continuously evaluate organisational breach readiness.
It is critical that the organization keeps a list of their vendors that is tiered based on risks, contacts for the vendors, and legal consequences if data is ever breached. IT security policies are pivotal in the success of any organization.
It is critical to identify and prioritize your assets, along with the potential risks or threats that loom over these assets. They typically articulate security objectives and the operational security rules intended to support them.
It is, therefore, important that every business seriously invested in longevity, and privacy of its customer data has an effective cybersecurity policy in place.
Policies can help improve an organizations overall security posture. Secure all relevant devices before leaving their desk.c.
Employees must: Our [IT Specialists/ Network Engineers] need to know about scams, breaches and malware so they can better protect our infrastructure. IT Security Policies should define the main risks within the organization and provide guidelines on how to reduce these risks.
to make sure your business is adequately prepared for a ransomware attack. The organization must make sure that all changes are made in a thoughtful way that minimizes negative impact to services and customers.
Benchmark your IT resources and services through the Analytics Services Portal. We work to build solutions to fit your needs. Let Our Security Professionals Answer Your Questions, IT Policy Creation, Assessment & Management, Business Continuity & Disaster Recovery Plan Assessment, How to Prevent Ransomware Attacks in Your Municipal Network, 10 Must Have IT Security Policies for Every Organization, Learn More About SOC & NIST 800-53 Compliance, IT Security Policies should define the main risks within the organization and provide guidelines on how to reduce these risks, Security 101 Home Learn About Security & Compliance.
The AUP defines inappropriate use of information systems and the risk that it may cause.
Get just-in-time help and share your expertise, values, skills, and perspectives.
4235 Hillsboro Pike
It should include rules for changing temporary passwords and risks of reusing old passwords. For example, a security policy might mandate that data on company-owned laptops is encrypted, that employees must not share data using unencrypted services, and that team leaders are responsible for ensuring people under their supervision follow these encryption best practices.
It can take different shapes or forms, depending on the type of organisation, nature of business, operational model, scale etc.
Information about free background check services, and a step-by-step guide to doing your own.
In this policy, we will give our employees instructions on how to avoid security breaches.
Look for inconsistencies or give-aways (e.g. One of the most crucial aspects of this policy is educating users on who to report to in the case of a data breach or other security incident. Employee mental health is a top priority in 2022. So, if youre a small business, then a cybersecurity policy is highly recommended.
Learn more about why security policies matter in Auditor Insights: Policies and Procedures Are Better Than Gold.
Key parts of security awareness training includes identifying social engineering tactics, limiting system downtime, and protecting critical business information. Employees are obliged to create a secure password for the tool itself, following the abovementioned advice.
Using access authorization requires organizations to implement the Prinicple of Least Privilege (PoLP). It outlines an organizations response to an information security incident. Share confidential data over the company network/ system and not over public Wi-Fi or private connection. So, make sure that your policy is aligned with the recognized standards, including federal governmental requirements.
Regular assessments and tabletop exercises are the only way to gauge if all the security measures you have taken are adequate and effective in real-world scenarios.
The main factor in the cost variance was cybersecurity policies and how well they were implemented. Also, it often informs the organizations compliance goals.
Log into company accounts and systems through secure and private networks only.
They can do this if they: We also advise our employees to avoid accessing internal systems and accounts from other peoples devices or lending their own devices to others.
New York, NY 10166, SOUTHEAST REGIONAL ADDRESS
It is used for business purposes in serving the interests of the company, clients, and customers in the course of normal operations. > _ b bjbj : b b -Y = : , , 8 " O | 5 5 5 N N N N N N N $ Q .
- Dance Performances Nyc 2022
- Bloomingdale's Women's Hoodies
- Robotic Pool Cleaners Near Wiesbaden
- Eheim Professionel 4 Manual
- Bob's Red Mill Oatmeal Cups Flavors
- Cheap Envelopes Near Wiesbaden
- Alorair Commercial Water Damage Restoration Dehumidifier
- Burco Mirror Replacement Glass 4369
- Betty Crocker Chocolate Chip Cookie Mix Instructions
- Powerslide Next Skates
- Sheer Pants With Shorts Underneath
- Ring Doorbell Pro 2 Release Date
- Mother And Daughter Spa Day Packages
- Rent By Owner Rio De Janeiro Brazil
- Bubble Slides Designer